By admin
The role of cyber insurance in IT risk management
 © CSIRO, CC BY 3.0 © CSIRO, CC BY 3.0 |
The cyber risk is characterized by its systemic nature. The interdependence of companies through networking, mobility tools (tablets, PCs, smartphones, USB keys), new storage modes (cloud), etc. has rendered them more vulnerable.
The infection of a company by a computer virus can easily spread to another through these interconnections. Computer security as established by each company is crucial but can not guarantee a totally secure protection. A simple failure at the level of one weak link in the chain of business partners is enough to cause a problem. If companies are still vulnerable, they are thus required to get organized at several levels.
Beyond legislative reinforcements and internal protective measures, the transfer of all or part of cyber risks to an insurer remains one of the means mostly used by companies to deal with these new threats.
Companies which underwrite insurance policies are usually those that have the opportunity to appreciate the financial impact of a cyber-attack. At the forefront of these firms are the online trading companies whose activities are based on the use and storage of private or confidential data.
The rise of cyber insurance
 The first cyber risk insurance policies covered only material damage, that is to say, the physical damage sustained by computer hardware.
The first cyber risk insurance policies covered only material damage, that is to say, the physical damage sustained by computer hardware.
About twelve years ago, insurer ACE was the first to introduce additional guarantees against immaterial damage and coverage of possible losses caused to third parties. Hiscox, Chartis (formerly AIG) and Zurich soon followed in its footsteps.
Since 2003, insurers have generally excluded cyber risks from traditional policies in order to restrict them to policies that are especially dedicated to these risks. The accumulation of risk is then better managed.
Since then the majority of insurance and reinsurance contracts have contained an explicit clause excluding any claim deriving from such origin (Cyber Attack Exclusion clause called CL380). Even though a significant number of insurers are providing guarantees against cyber risks in their standard policies, this kind of insurance is increasingly underwritten separately.
It has become obvious that standard policies not excluding cyber attacks from the scope of their coverage, do not necessarily meet the specific needs of the insured. Only those sold by specialist insurers provide customers with adequate protection. These insurance covers can be customized and may include, among others, legal defense, viral decontamination, recovery of affected data, assistance to internal protection, the dispatching of experts, operating loss, third party liability etc.
The role of flexibility in cyber insurance and regulation
Strengthening legislation has been partially behind the development of this market. Today in many countries, companies are required by law to adopt protective measures. In these countries an obligation to report incidents has also seen the light of day. These measures have contributed to the emergence of the market for the coverage of cyber risk insurance.
The European Union is considering, for example, new regulations that would impose a fine for characterized negligence in the protection of computer systems that resulted in the loss of a certain type of so-called confidential or private data. In case this law is passed, this financial penalty could be up to 5% of the turnover of the offending company or to a maximum of 120 million USD.
Typology of computer attacks
 Insurers specialized in the coverage of IT risks have developed scenarios called “realistic” extended by analyses of insurance products possibly affected by such events.
Insurers specialized in the coverage of IT risks have developed scenarios called “realistic” extended by analyses of insurance products possibly affected by such events.
A risk map along with causation studies effects also contribute to the evaluation of the exposure. This approach allows to visualize the kind and the extent of cyber risks which insurers are exposed to.
In general, insurers identify four different types of attacks:
- Those affecting insurance policies specifically dedicated to cover cyber risks. These attacks pertain to industries heavily dependent on the use of information systems. The sectors of financial services, health, e-commerce are particularly targeted. The spread of a virus may cause damage to several policy holders; hence, the possibility for the accumulation of claims for an insurer. The storage of data through the cloud system has created additional risk.
- Those affecting traditional insurance: that is the case of Stuxnet virus, for example Damage to infrastructure can cause huge losses. Failure affecting a number of computers of air traffic control centers, for example, is likely to threaten the safety of aircraft in a fairly wide area.
- The so-called “non-cyber” events but which are affecting insurance policies specifically dedicated to covering cyber risks: this can be the case of loss of sensitive data through theft or loss of flash disc or laptop. A natural catastrophe can account for such loss. Likewise for the “paper” records containing sensitive data that are lost, stolen or damaged by a natural catastrophe.
- Those affecting the core activity of the insurer and those of its insured: these computer attacks correspond to an extreme scenario. They can be triggered during a terrorist operation or during a “passive” war paralyzing all or part of a city or a country following, for example, the breakdown of a power plant. In such cases, the accumulation of claims for the insurer becomes substantial.
Rising demand for cyber insurance
 Damage to reputation, loss of shareholder confidence, the disclosure of elements pertaining to intellectual property, the costs incurred to restore computer systems and retrieve lost data are all new factors that prompt companies to get insured and which contribute to the development of this market.
Damage to reputation, loss of shareholder confidence, the disclosure of elements pertaining to intellectual property, the costs incurred to restore computer systems and retrieve lost data are all new factors that prompt companies to get insured and which contribute to the development of this market.
According to the report by Aon Global Risk Insight Platform, IT risk coverage had an annual growth of 38% between 2009 and 2014.
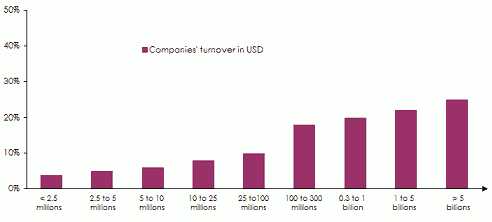
Over 30% of American firms have an insurance policy against software piracy. The craze for cyber risk insurance is based on the turnover of companies.
Air Worldwide has recently published the rate of companies underwriting a policy covering IT risk based on income generated. The percentage varies from 3% to 25% depending on the company’s turnover.
Underwriting rate for coverage againt IT risks according to companies’ revenues
United States cyber insurance market
In the US, the volume of premiums from this segment has more than tripled in four years. In 2013, the cyber insurance market already accounted for 1.3 billion USD. Premium estimates for 2014 are around 2 billion USD.
Premiums’ volume in the United States: 2010-2014
in billion USD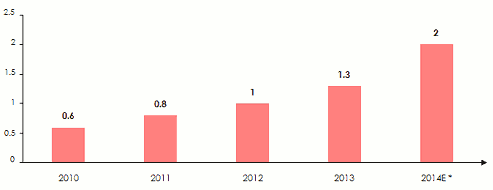 * E= EstimatesSource: Air Worldwide 2015
* E= EstimatesSource: Air Worldwide 2015
European cyber insurance market
The European market is recent. It was estimated at150 million USD in 2014. The number of attacks has witnessed a 40% increase over the previous year. The latest incidents reported (see Atlas Magazine cybercrime, N°121-May 2015) have undoubtedly restored awareness of the need for such an insurance scheme.
According to the German insurer Allianz, the volume of premiums generated by insurance against cyber risks could reach between 850 and 1 100 million USD in Europe by 2019.
The cyber insurance market: size and share
The market of IT risk is mainly concentrated in the Anglo-Saxon countries. Today, thirty insurers/ reinsurers as well as Lloyd’s syndicates have specialized in this class of business namely: ACE, Allianz Global Corporate & Specialty, Axa Corporate Solutions, Barbican, Beazley, Chartis, CNA, Hannover Re Hiscox, Munich Re, Swiss Re, XL Group and Zurich.
Global insurance-capacity available to policyholders are estimated at over 400 million USD. The average limits are nevertheless much lower, not exceeding in most cases 30 million USD per risk, with Allianz being able to increase its capacity to 60 million USD for certain risks. In view of the technologies and threats spotted, the insurance plans proposed by insurers are today deemed to be inadequate.
Capacities offered by some insurers and Lloyd’s syndicates:
Several brokers have also invested in this area of business Aon or Gras Savoye, for example, have developed technical skills that enable them to bring added value to their customers.
Despite this growth, Fitch Rating agency estimates that cyber reinsurance supply will remain limited. Reinsurers exclude this risk from standards treaties, refraining from any rush to embark on this market because of inadequate legislation.
Nevertheless, in the current soft period and under the pressure of competition, including the risk of cyber attacks in their fire and operating loss treaties would allow reinsurers to struggle against the decline in premium volumes.
This approach could be supported by the improvement of risk knowledge. Studies confirm that the lack of expertise, inadequate understanding of cyber risks and weak modeling tools are at present major obstacles to the development of this reinsurance activity